Mastering Java EE: Building Enterprise Applications with Confidence
The World of Java EE
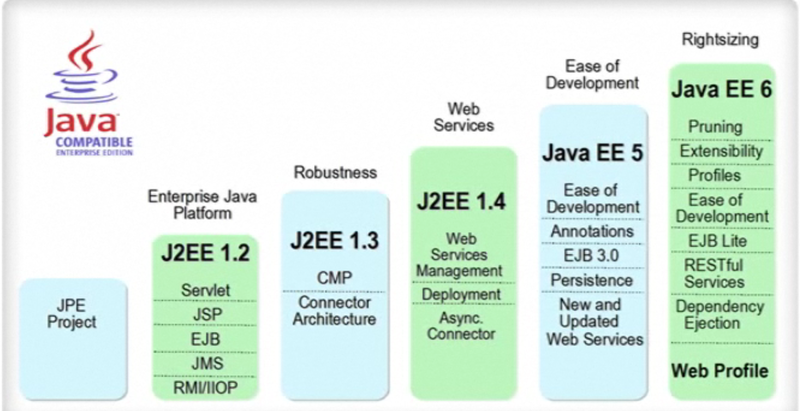
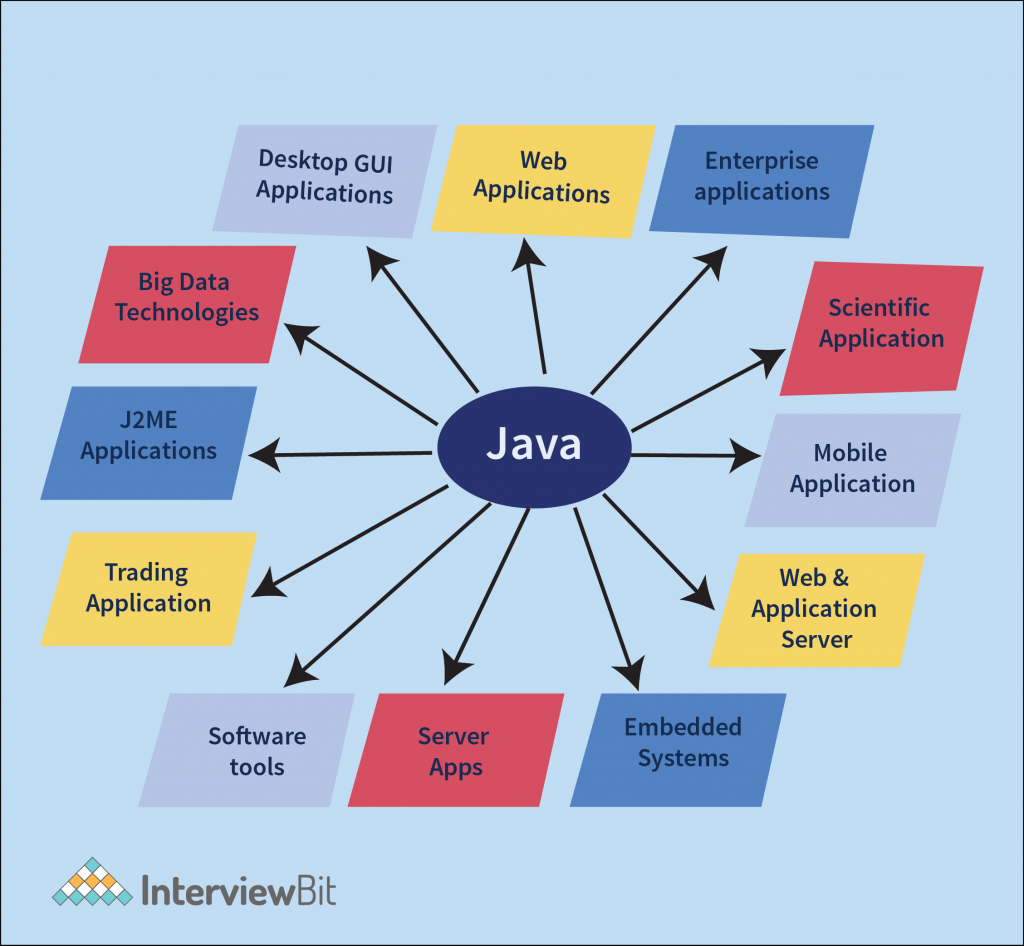
Java Platform, Enterprise Edition (Java EE), formerly known as J2EE, is a powerful platform for building enterprise-level applications. It provides a comprehensive set of APIs and services that simplify the development process and enable developers to create scalable, secure, and robust applications.
Key Features of Java EE
Java EE offers a range of features that make it a popular choice for developing enterprise applications:
- Component-based architecture: Java EE applications are built using components such as EJBs (Enterprise JavaBeans) and servlets, making it easier to manage and maintain large-scale projects.
- Enterprise services: Java EE provides essential services like transaction management, security, messaging, and more out of the box, saving developers time and effort in implementing these functionalities.
- Scalability: Java EE applications can be easily scaled to accommodate increased load by leveraging features like clustering and load balancing.
- Security: With built-in security mechanisms such as authentication and authorization, Java EE helps developers create secure applications that protect sensitive data.
- JPA (Java Persistence API): Java EE includes JPA for simplifying database operations by providing an object-relational mapping framework.
Popular Technologies in Java EE
Some of the well-known technologies within the Java EE ecosystem include:
- Servlets: Used for handling HTTP requests and responses in web applications.
- JSP (JavaServer Pages): Enables the creation of dynamic web content using Java code embedded in HTML pages.
- EJBs (Enterprise JavaBeans): Components that encapsulate business logic in enterprise applications.
- JMS (Java Message Service): Facilitates messaging between distributed components in an application.
The Future of Java EE
In recent years, there has been a shift towards microservices architecture and cloud-native development. As a response to these trends, Jakarta EE has emerged as the successor to Java EE. Jakarta EE continues to evolve with new features and enhancements to meet the demands of modern enterprise application development.
In conclusion, Java EE remains a robust platform for building enterprise-grade applications. Its rich set of features, scalability options, and security mechanisms make it a preferred choice for developers working on complex projects. By staying updated with the latest advancements in the ecosystem, developers can leverage the power of Java EE to create innovative solutions for businesses worldwide.
9 Key Advantages of Java EE for Enterprise Application Development
- Comprehensive set of APIs for building enterprise applications
- Built-in support for essential services like transaction management and security
- Scalability features such as clustering and load balancing
- Component-based architecture simplifies application development
- JPA simplifies database operations with object-relational mapping
- Robust security mechanisms for protecting sensitive data
- Support for messaging services through JMS (Java Message Service)
- Enables creation of dynamic web content with JSP (JavaServer Pages)
- Continuously evolving to meet the demands of modern enterprise application development
Challenges of Java EE: Navigating Complexity, Resource Demands, and Overhead
Comprehensive set of APIs for building enterprise applications
Java EE’s comprehensive set of APIs for building enterprise applications is a significant advantage that simplifies and accelerates the development process. By providing a wide range of pre-built functionalities and services, developers can focus on implementing business logic rather than reinventing the wheel. These APIs cover essential aspects such as security, transaction management, messaging, and more, enabling developers to create robust and scalable enterprise solutions efficiently. The availability of these APIs in Java EE streamlines development efforts, enhances code quality, and ultimately contributes to the successful delivery of complex enterprise applications.
Built-in support for essential services like transaction management and security
Java EE’s built-in support for essential services, such as transaction management and security, significantly simplifies the development process for enterprise applications. By providing robust mechanisms for handling transactions and ensuring data security, Java EE empowers developers to focus on building core functionalities without having to implement these critical features from scratch. This inherent support enhances the reliability and integrity of applications, making them more resilient to potential risks and ensuring a smoother user experience.
Scalability features such as clustering and load balancing
One of the key advantages of Java EE is its robust scalability features, including clustering and load balancing. By utilizing clustering, Java EE applications can be distributed across multiple servers, allowing for increased performance and fault tolerance. Load balancing ensures that incoming requests are evenly distributed among servers, optimizing resource utilization and enhancing system reliability. These scalability features in Java EE empower developers to build applications that can seamlessly handle growing workloads and provide a consistent user experience even under high traffic conditions.
Component-based architecture simplifies application development
The component-based architecture of Java EE simplifies application development by breaking down complex systems into smaller, reusable components. Developers can focus on building individual components with specific functionalities, making it easier to manage and maintain the codebase. This approach promotes code reusability, modularity, and scalability, allowing developers to create robust enterprise applications efficiently. By leveraging the component-based architecture of Java EE, developers can streamline the development process and enhance the overall quality of their applications.
JPA simplifies database operations with object-relational mapping
Java EE’s Java Persistence API (JPA) stands out as a valuable asset by simplifying database operations through object-relational mapping. This feature streamlines the interaction between Java objects and relational databases, eliminating the need for developers to write complex SQL queries manually. By providing a straightforward way to map Java classes to database tables and manage data persistence, JPA enhances productivity and efficiency in application development, ultimately saving time and effort for developers.
Robust security mechanisms for protecting sensitive data
Java EE offers robust security mechanisms designed to safeguard sensitive data within enterprise applications. By incorporating features such as authentication, authorization, encryption, and secure communication protocols, Java EE empowers developers to create secure environments that protect critical information from unauthorized access or breaches. These built-in security capabilities not only ensure compliance with industry standards and regulations but also instill trust in users by maintaining the confidentiality and integrity of data throughout the application lifecycle.
Support for messaging services through JMS (Java Message Service)
Java EE’s support for messaging services through JMS (Java Message Service) is a significant advantage for developers building enterprise applications. JMS provides a reliable and asynchronous communication mechanism that allows different components of an application to exchange messages seamlessly. By leveraging JMS in Java EE, developers can design robust and scalable systems that facilitate efficient communication between distributed components, enhancing the overall performance and reliability of the application.
Enables creation of dynamic web content with JSP (JavaServer Pages)
One of the key advantages of Java EE is its ability to enable the creation of dynamic web content through JavaServer Pages (JSP). JSP allows developers to seamlessly integrate Java code within HTML pages, making it easier to generate dynamic content based on user input or system data. This feature not only enhances the user experience by providing interactive web applications but also simplifies the development process by allowing for efficient and flexible content generation.
Continuously evolving to meet the demands of modern enterprise application development
Java EE’s ability to continuously evolve to meet the demands of modern enterprise application development sets it apart as a dynamic and forward-thinking platform. By adapting to emerging technologies and trends, Java EE ensures that developers have access to the latest tools and features needed to create innovative solutions for complex business requirements. This proactive approach not only enhances the platform’s capabilities but also enables developers to stay ahead in a rapidly changing technological landscape, making Java EE a reliable choice for building scalable and future-proof enterprise applications.
Steep learning curve
One significant drawback of Java EE is its steep learning curve. The platform encompasses a complex ecosystem with a plethora of APIs and technologies, creating a daunting challenge for newcomers to fully comprehend all the intricate concepts. Navigating through the vast array of components and understanding how they interact can be overwhelming, requiring a considerable investment of time and effort to become proficient in Java EE development.
Resource-intensive
Java EE applications can pose a challenge in terms of resource consumption as they can be resource-intensive. This is primarily attributed to the overhead involved in managing components such as EJBs (Enterprise JavaBeans) and the complexities of the application server environment. The need for robust infrastructure and adequate resources to support these components may result in higher hardware requirements and operational costs, making it essential for developers to carefully optimize their Java EE applications to ensure efficient performance while balancing resource utilization.
Overhead
The comprehensive features and services offered by Java EE, while beneficial for complex enterprise applications, can introduce overhead that may be excessive for smaller or simpler projects. This additional complexity could potentially lead to performance issues as the system may be burdened with functionalities that are not essential for the project’s requirements. Careful consideration and optimization are necessary to strike a balance between leveraging the capabilities of Java EE and avoiding unnecessary overhead in order to ensure optimal performance in all types of projects.