Enhancing Data Protection: The Role of Cloud Web Security in Safeguarding Information
The Importance of Cloud Web Security
In today’s digital age, the use of cloud services has become ubiquitous in both personal and business environments. Cloud computing offers numerous benefits, such as scalability, cost-efficiency, and flexibility. However, with the increasing reliance on cloud-based solutions, ensuring the security of data and applications stored in the cloud has become a top priority.
Challenges in Cloud Web Security
One of the main challenges in cloud web security is the protection of sensitive information from unauthorized access and cyber threats. As data is transferred between users and cloud servers over the internet, there is a risk of interception by malicious actors. Additionally, vulnerabilities in cloud infrastructure or misconfigurations can expose data to potential breaches.
Best Practices for Cloud Web Security
To mitigate these risks and enhance cloud web security, organizations should implement best practices such as:
- Encryption: Encrypting data both at rest and in transit helps prevent unauthorized access.
- Access Control: Implementing strict access control measures ensures that only authorized users can interact with sensitive data.
- Regular Audits: Conducting regular security audits and assessments helps identify vulnerabilities and ensure compliance with security standards.
- Multi-Factor Authentication (MFA): Enforcing MFA adds an extra layer of security by requiring multiple forms of verification for user authentication.
- Security Monitoring: Continuous monitoring of cloud environments for suspicious activities or anomalies can help detect and respond to security incidents promptly.
The Future of Cloud Web Security
As technology continues to evolve, so do cyber threats. The future of cloud web security lies in adopting advanced technologies such as artificial intelligence (AI) and machine learning to proactively detect and mitigate security risks. Additionally, regulatory compliance requirements will drive organizations to prioritize data protection and privacy in their cloud strategies.
In conclusion, ensuring robust cloud web security is essential for safeguarding sensitive information and maintaining trust with users. By implementing best practices and staying informed about emerging threats, organizations can confidently embrace the benefits of cloud computing while mitigating potential risks.
Understanding Cloud Web Security: Key Differences, Pillars, and Examples
- What is the difference between cybersecurity and cloud security?
- What are the 4 pillars of cloud security?
- What is the difference between network security and cloud security?
- What are the four types of cloud security?
- What is cloud cyber security?
- What is web security cloud?
- What is an example of cloud security?
What is the difference between cybersecurity and cloud security?
When discussing cybersecurity and cloud security, it is important to understand the distinction between the two concepts. Cybersecurity encompasses the protection of all digital assets, including networks, systems, and data, from cyber threats such as malware, phishing attacks, and unauthorized access. On the other hand, cloud security specifically focuses on safeguarding data and applications stored in cloud environments from potential risks associated with cloud computing, such as data breaches, misconfigurations, and insider threats. While cybersecurity is a broader term that addresses overall digital security measures, cloud security hones in on securing specifically cloud-based resources and services to ensure confidentiality, integrity, and availability of data in the cloud.
What are the 4 pillars of cloud security?
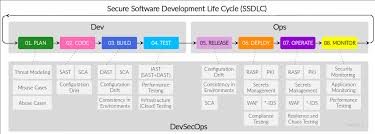
The 4 pillars of cloud security encompass key principles that organizations should prioritize to ensure robust protection of their cloud environments. These pillars include data security, compliance, identity and access management, and security governance. Data security focuses on encrypting data, implementing access controls, and monitoring for unauthorized access. Compliance involves adhering to industry regulations and standards to protect sensitive information. Identity and access management emphasize controlling user privileges and authentication mechanisms. Security governance entails establishing policies, procedures, and controls to manage risks effectively in the cloud environment. By addressing these four pillars comprehensively, organizations can enhance their cloud security posture and mitigate potential threats effectively.
What is the difference between network security and cloud security?
When comparing network security and cloud security, it is important to understand that while both focus on protecting data and systems, they operate in different contexts. Network security primarily deals with securing the network infrastructure itself, including devices, servers, and connections within an organization’s on-premises network. On the other hand, cloud security is specifically tailored to safeguarding data and applications stored in cloud environments managed by third-party providers. Cloud security addresses unique challenges such as data encryption, access control in shared environments, and compliance with cloud-specific regulations. While network security focuses on internal threats and perimeter defenses, cloud security expands its scope to address risks associated with remote access, multi-tenancy, and data migration across cloud platforms. Ultimately, understanding the distinctions between network security and cloud security is crucial for organizations to implement comprehensive cybersecurity measures that cover both their traditional network infrastructure and their cloud-based resources effectively.
What are the four types of cloud security?
When discussing cloud web security, it is essential to understand the four main types of cloud security measures that organizations can implement to protect their data and applications. These include network security, data security, identity management, and compliance. Network security focuses on securing the network infrastructure to prevent unauthorized access and cyber attacks. Data security involves encrypting data at rest and in transit to safeguard sensitive information from breaches. Identity management ensures that only authorized users can access resources within the cloud environment. Compliance measures address regulatory requirements and industry standards to maintain data privacy and integrity in the cloud. By implementing these four types of cloud security measures effectively, organizations can enhance their overall cybersecurity posture and mitigate potential risks.
What is cloud cyber security?
Cloud cybersecurity refers to the practices and technologies implemented to protect cloud-based systems, data, and infrastructure from cyber threats. It encompasses a range of security measures designed to safeguard sensitive information stored in the cloud from unauthorized access, data breaches, and other malicious activities. Cloud cybersecurity involves encryption, access controls, threat detection, incident response protocols, and compliance with industry regulations to ensure the confidentiality, integrity, and availability of data in cloud environments. By employing robust cybersecurity measures in the cloud, organizations can enhance their overall security posture and mitigate risks associated with storing and processing data in remote servers.
What is web security cloud?
Web security cloud, also known as cloud web security, refers to the practice of protecting websites and web applications hosted in the cloud from cyber threats and unauthorized access. It involves implementing security measures such as encryption, access control, and monitoring to ensure the confidentiality, integrity, and availability of data stored in the cloud. Web security cloud solutions help organizations defend against various threats, including malware, phishing attacks, and data breaches, by leveraging advanced technologies and best practices to secure their online assets effectively. By prioritizing web security in the cloud environment, businesses can safeguard their digital presence and maintain trust with users while harnessing the benefits of cloud computing.
What is an example of cloud security?
An example of cloud security is the use of encryption to protect data stored in cloud environments. Encryption involves encoding data in a way that only authorized parties with the decryption key can access it. By encrypting sensitive information before uploading it to the cloud, organizations can ensure that even if the data is intercepted, it remains unreadable and secure. This practice enhances the overall security of cloud storage and mitigates the risk of unauthorized access to confidential data.