Unlocking Success with Reliable Tech Solutions
The Importance of Reliable Tech Solutions
In today’s fast-paced digital world, reliable technology solutions play a crucial role in the success of businesses and individuals alike. Whether it’s managing data, communicating with clients, or streamlining processes, having dependable tech solutions is essential for efficiency and growth.
Enhanced Productivity
Reliable tech solutions contribute to enhanced productivity by ensuring that systems run smoothly without frequent disruptions. When technology works seamlessly, employees can focus on their tasks without being hindered by technical issues or downtime.
Improved Customer Experience
For businesses, providing a seamless customer experience is paramount. Reliable tech solutions enable companies to deliver consistent service to their customers, whether through online transactions, customer support systems, or personalized interactions.
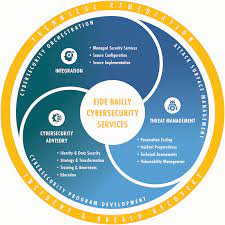
Data Security
Data security is a top concern for organizations in today’s digital landscape. Reliable tech solutions incorporate robust security measures to protect sensitive information from cyber threats and unauthorized access. By investing in secure technology solutions, businesses can safeguard their data assets and maintain trust with customers.
Scalability and Flexibility
Scalability and flexibility are key features of reliable tech solutions. As businesses grow and evolve, they need technology that can adapt to changing needs and demands. Scalable solutions allow organizations to expand their operations without significant disruptions or costly upgrades.
Cost-Efficiency
While investing in reliable tech solutions may require an initial outlay, the long-term benefits often outweigh the costs. By reducing downtime, increasing efficiency, and improving overall performance, reliable technology solutions can lead to cost savings in the long run.
In conclusion, reliable tech solutions are essential for modern businesses seeking to stay competitive in a rapidly evolving digital landscape. By prioritizing reliability in technology investments, organizations can drive productivity, enhance customer experiences, ensure data security, achieve scalability, and realize cost-efficiency.
Understanding the Importance and Benefits of Reliable Tech Solutions: FAQs Answered
- What are reliable tech solutions?
- Why are reliable tech solutions important for businesses?
- How do reliable tech solutions enhance productivity?
- What role do reliable tech solutions play in data security?
- How can reliable tech solutions improve customer experience?
- What features make a tech solution reliable?
- Are scalable and flexible tech solutions important for reliability?
- What are the cost benefits of investing in reliable tech solutions?
What are reliable tech solutions?
Reliable tech solutions refer to dependable and trustworthy technological tools, systems, and services that consistently perform as intended without unexpected failures or disruptions. These solutions are designed to meet the needs of businesses and individuals by providing stable performance, secure data handling, scalability to accommodate growth, and flexibility to adapt to changing requirements. In essence, reliable tech solutions are the foundation of efficient operations, enhanced productivity, improved customer experiences, and overall success in today’s digital age.
Why are reliable tech solutions important for businesses?
Reliable tech solutions are crucial for businesses due to their significant impact on operational efficiency, customer satisfaction, and data security. By relying on dependable technology, businesses can streamline processes, minimize downtime, and maximize productivity. Consistent and stable tech solutions also play a key role in enhancing the overall customer experience, ensuring seamless interactions and transactions. Moreover, the robust security measures integrated into reliable tech solutions help safeguard sensitive data from cyber threats, protecting both the business and its customers. In essence, investing in reliable tech solutions is essential for businesses to maintain competitiveness, build trust with customers, and achieve long-term success in today’s digital landscape.
How do reliable tech solutions enhance productivity?
Reliable tech solutions enhance productivity by providing a stable and efficient environment for users to carry out their tasks seamlessly. When technology functions reliably without constant interruptions or downtime, employees can focus on their work without disruptions, leading to increased efficiency and output. By streamlining processes, automating repetitive tasks, and ensuring quick access to necessary resources, reliable tech solutions empower individuals and teams to work more effectively and achieve their goals in a timely manner. This enhanced productivity not only benefits the workforce but also contributes to overall business success by optimizing operations and maximizing output.
What role do reliable tech solutions play in data security?
Reliable tech solutions play a critical role in data security by providing robust mechanisms to safeguard sensitive information from cyber threats and unauthorized access. From encryption protocols to secure authentication methods, dependable technology ensures that data remains protected at all times. By integrating reliable tech solutions into their infrastructure, organizations can establish a strong defense against potential breaches and mitigate risks associated with data compromise. Ultimately, the reliability of tech solutions directly influences the integrity and confidentiality of data, reinforcing the foundation of trust between businesses and their stakeholders.
How can reliable tech solutions improve customer experience?
Reliable tech solutions play a vital role in enhancing customer experience by ensuring consistent and seamless interactions. When technology functions reliably, businesses can provide efficient customer support, personalized services, and smooth online transactions. Reliable tech solutions enable companies to respond promptly to customer inquiries, deliver products and services on time, and maintain a secure digital environment for transactions. By building trust through reliable technology, businesses can create positive experiences that result in satisfied customers who are more likely to return and recommend the brand to others.
What features make a tech solution reliable?
When evaluating the reliability of a tech solution, several key features come into play. Firstly, robust security measures are essential to protect data and systems from cyber threats. Additionally, seamless performance and minimal downtime contribute to reliability by ensuring consistent operation. Scalability and flexibility allow the solution to adapt to changing needs over time without compromising functionality. Regular updates and maintenance also play a crucial role in keeping the technology up-to-date and running smoothly. Ultimately, a reliable tech solution combines security, performance, adaptability, and maintenance to provide users with a dependable and efficient experience.
Are scalable and flexible tech solutions important for reliability?
Scalable and flexible tech solutions are indeed crucial components of reliability in the realm of technology. The ability of a system to scale and adapt to changing needs and demands directly impacts its reliability. A scalable solution ensures that as an organization grows or experiences fluctuations in workload, the technology can expand seamlessly without compromising performance or stability. Similarly, flexibility allows for adjustments to be made swiftly in response to evolving requirements, ensuring that the tech solution remains relevant and efficient over time. Together, scalability and flexibility contribute significantly to the overall reliability of a tech solution by enabling it to meet current and future needs effectively.
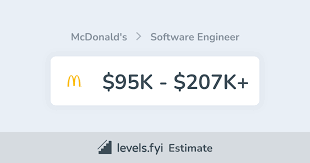
What are the cost benefits of investing in reliable tech solutions?
Investing in reliable tech solutions offers significant cost benefits for businesses. While the initial investment may seem higher, the long-term savings are substantial. Reliable technology reduces downtime, which can lead to increased productivity and revenue generation. By minimizing technical issues and system failures, businesses can avoid costly disruptions and maintain operational efficiency. Additionally, reliable tech solutions often require less maintenance and support, resulting in lower ongoing expenses. Ultimately, the cost benefits of investing in reliable technology solutions extend beyond financial savings to include improved performance, enhanced security, and better scalability for future growth.