Exploring the Significance of Prototyping in Software Engineering
The Importance of Prototyping in Software Engineering
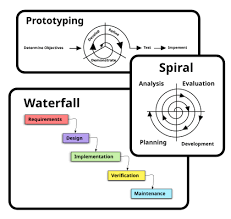
Prototyping is a crucial phase in the software development process that allows developers to create a preliminary version of a product to gather feedback, test functionality, and identify potential issues before moving forward with full-scale development.
Benefits of Prototyping
Enhanced Collaboration: Prototypes provide a visual representation of the final product, facilitating better communication and collaboration between stakeholders, developers, and designers.
Risk Mitigation: By testing a prototype early in the development cycle, teams can identify and address potential challenges, reducing the risk of costly errors later on.
User Feedback: Prototypes allow developers to gather feedback from users and stakeholders, enabling them to make informed decisions about the product’s features and functionality.
Types of Prototypes
Throwaway Prototype: A quick and inexpensive prototype used to explore design ideas and concepts without the intention of being part of the final product.
Evolutionary Prototype: A prototype that evolves through iterations based on user feedback and testing until it becomes the final product.
Best Practices for Prototyping
- Define Objectives: Clearly outline the goals and objectives of the prototype to ensure it aligns with the project requirements.
- User-Centered Design: Focus on creating prototypes that prioritize user experience and usability.
- Rapid Iteration: Iterate quickly based on feedback to refine the prototype efficiently.
- Cross-Functional Collaboration: Involve stakeholders from different disciplines to gather diverse perspectives during prototyping.
- Evaluate Effectiveness: Assess the success of the prototype based on predefined criteria to determine its impact on project goals.
In Conclusion
Prototyping plays a vital role in software engineering by enabling teams to validate ideas, improve collaboration, mitigate risks, and deliver user-centered products. By incorporating prototyping into their development process, organizations can enhance innovation, reduce costs, and ultimately create successful software solutions that meet user needs effectively.
5 Key Benefits of Prototyping in Software Engineering: Enhancing Feedback, Communication, and Risk Management
- Allows for early feedback from stakeholders and users
- Helps identify and address potential issues before full-scale development
- Facilitates better communication and collaboration among team members
- Reduces project risks by validating concepts and requirements early on
- Enables rapid iteration and refinement of the product based on feedback
7 Challenges of Prototyping in Software Engineering: From Time and Cost to Misinterpretation and Technical Debt
- 1. Time-Consuming
- 2. Costly
- 3. Scope Creep
- 4. Misinterpretation
- 5. Technical Debt
- 6. Resource Intensive
- 7. Ineffective Feedback
Allows for early feedback from stakeholders and users
One significant advantage of prototyping in software engineering is its ability to facilitate early feedback from stakeholders and users. By creating a preliminary version of the software product, developers can present it to stakeholders and users for evaluation and input at an early stage. This feedback loop enables teams to gather valuable insights, identify potential issues, and make necessary adjustments before proceeding with full-scale development. Incorporating feedback from stakeholders and users during the prototyping phase helps ensure that the final product meets their requirements and expectations, leading to higher user satisfaction and overall project success.
Helps identify and address potential issues before full-scale development
Prototyping in software engineering is a valuable practice as it aids in the early identification and resolution of potential issues before committing to full-scale development. By creating a preliminary version of the product, developers can test its functionality, gather feedback, and pinpoint any challenges or shortcomings. This proactive approach not only helps in mitigating risks but also saves time and resources by addressing issues at a stage where modifications are more manageable. Ultimately, the ability to identify and address potential issues through prototyping contributes to the overall success and quality of the final software product.
Facilitates better communication and collaboration among team members
Prototyping in software engineering facilitates better communication and collaboration among team members by providing a visual representation of the product that all stakeholders can interact with. This tangible prototype serves as a common point of reference, allowing developers, designers, and other team members to align their understanding of the project goals and requirements. Through active participation in the prototyping process, team members can share ideas, provide feedback, and make informed decisions collaboratively, leading to a more cohesive and effective development effort.
Reduces project risks by validating concepts and requirements early on
One significant advantage of prototyping in software engineering is its ability to reduce project risks by validating concepts and requirements early in the development process. By creating a prototype, developers can test the feasibility of ideas, gather feedback from stakeholders, and ensure that the project aligns with the desired objectives. This proactive approach helps identify potential issues and challenges at an early stage, allowing teams to make informed decisions and adjustments before investing significant time and resources into full-scale development. Ultimately, this practice minimizes uncertainties, enhances project success rates, and contributes to delivering high-quality software solutions that meet user expectations effectively.
Enables rapid iteration and refinement of the product based on feedback
One significant advantage of prototyping in software engineering is its ability to facilitate rapid iteration and refinement of the product through feedback. By creating prototypes that can be easily modified and tested, developers can quickly gather input from users and stakeholders to identify areas for improvement. This iterative process allows for timely adjustments to be made, ensuring that the final product meets the desired requirements and user expectations effectively.
1. Time-Consuming
One significant drawback of prototyping in software engineering is its time-consuming nature. Developing prototypes often demands a considerable amount of time, particularly when multiple iterations are necessary to refine the design and functionality. This extended timeline can delay the overall development process and impact project deadlines, leading to potential setbacks in delivering the final product to clients or users. The iterative nature of prototyping, while beneficial for improving the end product, can also contribute to increased development time and resource allocation, posing a challenge for teams aiming to streamline their workflow and meet project milestones efficiently.
2. Costly
One significant drawback of prototyping in software engineering is its costliness. Developing and evaluating prototypes can lead to increased expenses, especially for intricate projects. The resources required to design, build, and test prototypes, along with the time invested in iteration and refinement processes, can contribute to a higher overall project budget. This financial burden may pose challenges for organizations with limited resources or strict budget constraints, making cost management a crucial consideration when deciding whether to incorporate prototyping into the software development cycle.
3. Scope Creep
Scope creep is a significant con associated with prototyping in software engineering. While prototypes are intended to provide a preliminary version of the product for feedback and testing, they can sometimes lead to an increase in scope as stakeholders suggest new features or modifications during the prototyping phase. This can result in project delays, increased costs, and potential deviations from the original project objectives. Managing scope creep effectively during the prototyping process is essential to ensure that the final product remains aligned with the initial project scope and goals.
4. Misinterpretation
In software engineering, one significant drawback of prototyping is the potential for misinterpretation by stakeholders. Due to the visual nature of prototypes, there is a risk that stakeholders may perceive them as final products rather than preliminary models. This misinterpretation can set unrealistic expectations regarding the project’s progress and features, ultimately leading to dissatisfaction when the final product does not align with the prototype. Effective communication and clear documentation are essential to manage stakeholder expectations and ensure that prototypes are viewed as iterative tools for feedback and improvement rather than finished solutions.
5. Technical Debt
Rushed prototyping in software engineering can lead to the accumulation of technical debt, which refers to the additional time and effort required to fix issues or improve code quality that were overlooked during the prototyping phase. When developers prioritize speed over thoroughness in prototyping, they may end up implementing quick solutions that are not scalable or maintainable in the long run. This technical debt can slow down future development cycles, increase the risk of errors, and hinder the overall efficiency of the software project. Addressing technical debt incurred from rushed prototyping requires dedicated resources and time, diverting attention from new features or improvements that could enhance the software’s functionality.
6. Resource Intensive
Prototyping in software engineering can pose challenges due to its resource-intensive nature. Developing prototypes demands dedicated resources such as time, specialized expertise, and appropriate tools, which can strain project resources. Allocating these resources for prototyping activities may impact the overall project timeline and budget, potentially leading to delays or increased costs. Therefore, careful planning and resource management are essential to mitigate the impact of this con and ensure that prototyping efforts align with project goals effectively.
7. Ineffective Feedback
In software engineering, one significant drawback of prototyping is the risk of ineffective feedback. When feedback on prototypes is not collected or analyzed properly, it can lead to a lack of valuable insights for enhancing the final product. Without thorough evaluation and interpretation of feedback, developers may miss crucial opportunities to address user needs and improve functionality, potentially resulting in a final product that does not meet expectations or requirements. Effective feedback collection and analysis are essential to ensure that prototyping efforts contribute meaningfully to the overall success of a software project.