Driving Innovation Through Sustainable Software Development Practices
The Importance of Sustainable Software Development
In today’s rapidly evolving technological landscape, the concept of sustainability is not limited to environmental concerns. Sustainable software development has emerged as a crucial aspect of creating long-lasting and impactful digital solutions.
So, what exactly is sustainable software development? It refers to the practice of designing, building, and maintaining software applications in a way that minimizes negative impacts on the environment, society, and the economy while maximizing positive outcomes.
Key Principles of Sustainable Software Development
- Efficiency: Writing efficient code that consumes fewer resources such as memory and processing power can contribute to reducing energy consumption.
- Scalability: Designing software that can adapt to changing needs and accommodate growth without significant rework helps in extending the lifespan of applications.
- Resilience: Building resilient software that can withstand failures and disruptions not only enhances user experience but also reduces the need for frequent updates and replacements.
- Transparency: Being transparent about the environmental impact of software development practices can raise awareness and promote more sustainable approaches within the industry.
- Circular Economy: Embracing principles of circular economy by reusing components, recycling code, and minimizing waste can contribute to a more sustainable software ecosystem.
The Benefits of Sustainable Software Development
By adopting sustainable practices in software development, organizations can reap numerous benefits:
- Cost Savings: Efficient use of resources leads to cost savings in terms of energy consumption, infrastructure maintenance, and operational expenses.
- Innovation: Focusing on sustainability encourages innovation in design and development processes, leading to creative solutions that address both environmental and business challenges.
- Competitive Advantage: Demonstrating a commitment to sustainability can enhance brand reputation, attract environmentally conscious customers, and give organizations a competitive edge in the market.
- Long-Term Viability: Sustainable software solutions are more likely to remain relevant and functional over time, reducing the need for frequent upgrades or replacements.
In Conclusion
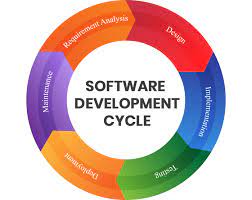
Sustainable software development is not just a trend but a necessity in today’s digital age. By integrating sustainability principles into the entire software development lifecycle, organizations can create resilient, efficient, and future-proof solutions that benefit both their business objectives and the planet as a whole.
7 Essential Tips for Sustainable Software Development
- Write efficient code to reduce energy consumption.
- Minimize server usage by optimizing resource allocation.
- Use version control to track changes and collaborate efficiently.
- Prioritize modular and scalable design for easier maintenance and updates.
- Implement automated testing to catch bugs early and improve overall software quality.
- Consider the environmental impact of data storage and choose eco-friendly options.
- Regularly review and refactor code to improve performance and sustainability.
Write efficient code to reduce energy consumption.
Writing efficient code is a key tip in sustainable software development as it directly contributes to reducing energy consumption. By optimizing algorithms, minimizing resource usage, and improving code performance, developers can create software that operates more efficiently, requiring less processing power and thereby lowering the overall energy consumption of the system. This not only benefits the environment by reducing carbon emissions but also leads to cost savings for organizations in terms of energy bills and infrastructure maintenance. Efficient code is a fundamental aspect of creating sustainable software solutions that are both environmentally friendly and economically viable in the long run.
Minimize server usage by optimizing resource allocation.
To promote sustainable software development, it is essential to minimize server usage by optimizing resource allocation. By efficiently allocating resources on servers, such as memory and processing power, developers can reduce energy consumption and minimize the environmental impact of running software applications. This practice not only contributes to cost savings but also aligns with the principles of sustainability by ensuring that resources are used effectively and responsibly. By prioritizing resource optimization, software developers can create more efficient and eco-friendly solutions that support a greener digital ecosystem.
Use version control to track changes and collaborate efficiently.
Utilizing version control systems is a crucial tip in sustainable software development as it allows developers to track changes, manage code revisions, and collaborate efficiently across teams. By maintaining a centralized repository of code versions, developers can easily revert to previous iterations, identify and resolve issues, and ensure consistency in the development process. This practice not only enhances productivity but also promotes transparency and accountability within the development workflow, contributing to the overall sustainability of software projects.
Prioritize modular and scalable design for easier maintenance and updates.
To promote sustainable software development, it is essential to prioritize modular and scalable design. By breaking down software components into modular units that can be easily maintained and updated independently, developers can streamline the maintenance process and facilitate future updates. This approach not only improves the longevity of the software but also enhances its adaptability to evolving requirements, ultimately reducing the environmental impact associated with frequent overhauls or replacements.
Implement automated testing to catch bugs early and improve overall software quality.
Implementing automated testing in software development is a key strategy for promoting sustainability. By catching bugs early in the development process, automated testing helps improve overall software quality and reliability. This proactive approach not only reduces the time and effort required for bug fixing but also minimizes the environmental impact associated with rework and inefficient coding practices. Embracing automated testing not only enhances the efficiency of software development but also contributes to building more sustainable digital solutions that can adapt to changing needs and minimize resource consumption over time.
Consider the environmental impact of data storage and choose eco-friendly options.
When focusing on sustainable software development, it is essential to consider the environmental impact of data storage. Opting for eco-friendly options in data storage can significantly reduce the carbon footprint of software applications. By choosing energy-efficient storage solutions and implementing practices such as data deduplication and compression, developers can minimize resource consumption and contribute to a more sustainable digital ecosystem. Prioritizing eco-friendly data storage not only benefits the environment but also aligns with the principles of responsible and forward-thinking software development.
Regularly review and refactor code to improve performance and sustainability.
Regularly reviewing and refactoring code is a crucial practice in sustainable software development. By continuously assessing and optimizing the codebase, developers can enhance performance, reduce resource consumption, and ensure the long-term sustainability of the software. Refactoring allows for the elimination of redundant or inefficient code, making the application more efficient and easier to maintain. This proactive approach not only improves the overall quality of the software but also contributes to a more sustainable digital ecosystem by minimizing waste and maximizing efficiency.