Mastering Java App Development: Building Powerful Applications with Java
The Power of Java Applications
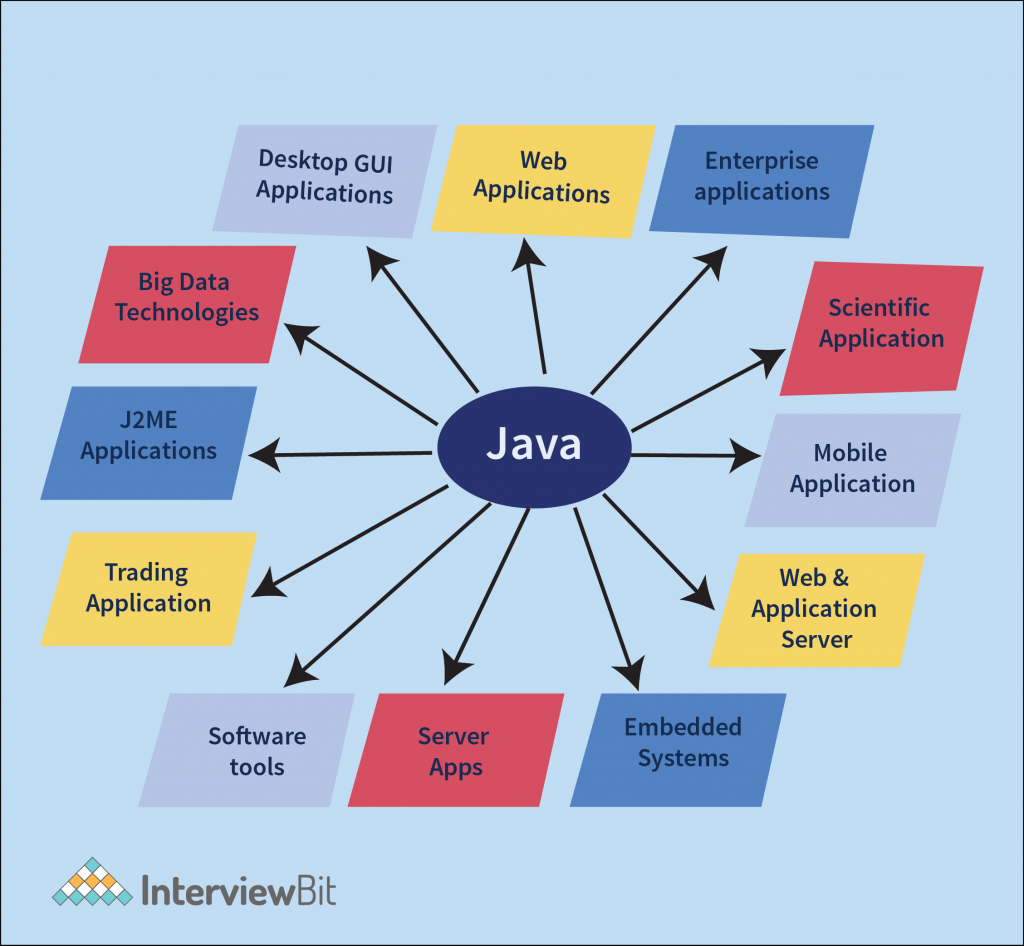
Java is a versatile programming language that has gained immense popularity for its ability to create robust and scalable applications. Java applications are used in a wide range of industries, from web development to mobile apps and enterprise software solutions.
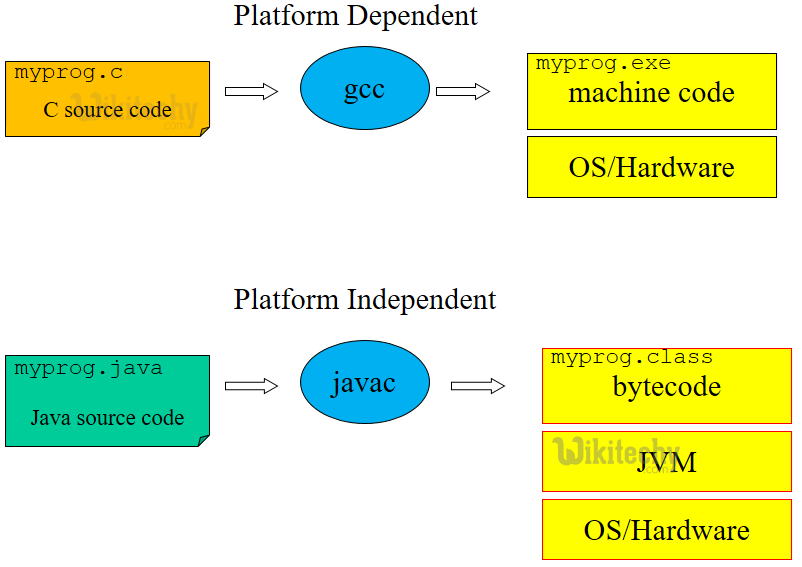
One of the key strengths of Java applications is their platform independence. This means that a Java application can run on any device or operating system that has a Java Virtual Machine (JVM) installed. This portability makes Java an ideal choice for developing cross-platform applications that reach a larger audience.
Java’s rich set of libraries and frameworks provide developers with the tools they need to build complex and feature-rich applications efficiently. Whether you are developing a simple desktop application or a sophisticated web-based system, Java offers the flexibility and scalability required to meet your project’s demands.
Furthermore, Java’s strong emphasis on security makes it a popular choice for developing secure applications. With built-in features like automatic memory management and strong type checking, Java helps developers write code that is less prone to common vulnerabilities such as buffer overflows or memory leaks.
Java’s community support is another factor that contributes to its popularity. The vast community of Java developers worldwide ensures that there are plenty of resources, tutorials, and forums available for developers looking to enhance their skills or troubleshoot issues they encounter during development.
In conclusion, Java applications offer unparalleled versatility, portability, security, and community support. Whether you are a seasoned developer or just starting your programming journey, exploring the world of Java applications can open up a world of possibilities for creating innovative and powerful software solutions.
9 Essential Tips for Building Robust and Maintainable Java Applications
- 1. Write clean and readable code to improve maintainability.
- 2. Follow naming conventions to enhance code consistency.
- 3. Use meaningful comments to explain complex logic or algorithms.
- 4. Break down large functions into smaller, reusable methods for better organization.
- 5. Implement error handling to gracefully manage exceptions and prevent crashes.
- 6. Optimize performance by avoiding unnecessary loops or operations.
- 7. Utilize design patterns to solve common problems effectively.
- 8. Test your application thoroughly with unit tests and integration tests.
- 9. Keep learning and stay updated with the latest Java features and best practices.
1. Write clean and readable code to improve maintainability.
Writing clean and readable code is crucial when developing Java applications to enhance maintainability. By following best practices and adhering to coding standards, developers can ensure that their code is easy to understand and modify in the future. Clean code not only makes it simpler for other team members to collaborate on the project but also reduces the chances of introducing bugs during maintenance. Prioritizing readability in code can lead to more efficient debugging, faster updates, and overall smoother development processes for Java applications.
2. Follow naming conventions to enhance code consistency.
Following naming conventions is a crucial practice in Java application development as it enhances code consistency and readability. By adhering to established naming conventions, developers can create code that is easier to understand and maintain. Consistent naming of classes, methods, variables, and other elements not only improves the overall quality of the codebase but also promotes collaboration among team members. When everyone follows the same naming conventions, it becomes simpler to navigate through the code, identify functionalities, and make modifications without confusion. This simple tip can have a significant impact on the efficiency and effectiveness of Java application development projects.
3. Use meaningful comments to explain complex logic or algorithms.
When developing a Java application, it is crucial to utilize meaningful comments to elucidate intricate logic or algorithms. By incorporating clear and concise comments within the codebase, developers can enhance the readability and maintainability of the application. These comments serve as valuable documentation for understanding the purpose behind complex logic, facilitating collaboration among team members, and aiding in future troubleshooting and modifications. Embracing this practice not only promotes code clarity but also contributes to the overall efficiency and effectiveness of the Java application development process.
4. Break down large functions into smaller, reusable methods for better organization.
Breaking down large functions into smaller, reusable methods is a valuable tip in Java application development. By dividing complex tasks into smaller, more manageable chunks, developers can improve the organization and maintainability of their code. This practice not only enhances readability but also promotes code reusability, making it easier to maintain and update the application in the future. Additionally, breaking down functions into smaller methods allows for better testing and debugging, as issues can be isolated and addressed more effectively. Overall, adopting this approach leads to more efficient and structured Java applications.
5. Implement error handling to gracefully manage exceptions and prevent crashes.
Implementing error handling is a crucial aspect of developing Java applications to ensure smooth operation and prevent unexpected crashes. By gracefully managing exceptions, developers can anticipate potential errors and handle them appropriately, maintaining the application’s stability and enhancing the user experience. Proper error handling not only helps in identifying issues promptly but also allows for effective troubleshooting and debugging, leading to more robust and reliable Java applications.
6. Optimize performance by avoiding unnecessary loops or operations.
To optimize the performance of a Java application, it is crucial to avoid unnecessary loops or operations. By minimizing the number of loops and streamlining operations within the code, developers can significantly improve the efficiency and speed of their application. Unnecessary loops can lead to increased processing time and resource consumption, impacting the overall performance of the software. Therefore, by carefully assessing and optimizing the logic within loops and operations, developers can enhance the performance of their Java application and deliver a more responsive user experience.
7. Utilize design patterns to solve common problems effectively.
Utilizing design patterns in Java applications is a valuable strategy to solve common problems effectively. By leveraging established design patterns such as Singleton, Factory, or Observer, developers can streamline their code structure, improve maintainability, and enhance scalability. Design patterns provide proven solutions to recurring design challenges, allowing developers to write cleaner and more efficient code while promoting best practices in software development. Incorporating design patterns in Java applications not only enhances code quality but also fosters a deeper understanding of software architecture principles among developers.
8. Test your application thoroughly with unit tests and integration tests.
Testing your Java application thoroughly with unit tests and integration tests is crucial for ensuring its reliability and functionality. Unit tests allow you to test individual components of your code in isolation, verifying that each part works as intended. On the other hand, integration tests help you assess how different parts of your application work together as a whole. By conducting both types of tests diligently, you can identify and address any issues early in the development process, leading to a more robust and stable Java application in the end.
9. Keep learning and stay updated with the latest Java features and best practices.
To ensure the success of your Java applications, it is crucial to continuously expand your knowledge and stay informed about the latest Java features and best practices. By keeping up with advancements in the Java ecosystem, you can leverage new tools, techniques, and optimizations to enhance the performance, security, and scalability of your applications. Embracing a mindset of lifelong learning in Java development not only sharpens your skills but also empowers you to adapt to industry trends and deliver cutting-edge solutions that meet evolving user needs.