Software Product Development: A Comprehensive Guide
Software Product Development: A Comprehensive Guide
In today’s digital age, software product development plays a crucial role in shaping businesses and industries. From innovative mobile apps to complex enterprise solutions, the process of creating software products requires a structured approach and a deep understanding of technology and user needs.
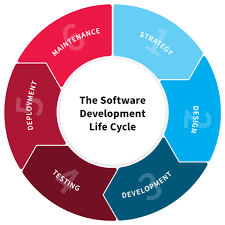
The Software Development Life Cycle (SDLC)
The Software Development Life Cycle (SDLC) is a systematic process that outlines the stages involved in developing software products. The typical phases of SDLC include:
- Planning: Defining project goals, requirements, and constraints.
- Analysis: Gathering and analyzing user needs and system requirements.
- Design: Creating a detailed design of the software architecture and user interface.
- Development: Writing code, testing functionality, and fixing bugs.
- Testing: Conducting various tests to ensure the software meets quality standards.
- Deployment: Releasing the software to users or clients.
- Maintenance: Providing ongoing support, updates, and enhancements.
Key Principles of Software Product Development
Successful software product development is guided by several key principles:
- User-Centric Design: Prioritizing user experience and usability throughout the development process.
- Agile Methodology: Embracing flexibility, collaboration, and iterative development cycles to adapt to changing requirements.
- Quality Assurance: Implementing rigorous testing procedures to ensure reliability, performance, and security.
- Scalability: Designing software products that can grow and evolve with the changing needs of users and businesses.
The Role of Technology in Software Product Development
Technology plays a pivotal role in driving innovation and efficiency in software product development. Emerging technologies such as artificial intelligence, cloud computing, Internet of Things (IoT), and blockchain are reshaping the way software products are designed, developed, and deployed.
Challenges in Software Product Development
Despite its benefits, software product development comes with its own set of challenges. Common challenges include managing project scope creep, meeting tight deadlines, ensuring cross-team collaboration, addressing cybersecurity threats, and keeping up with rapidly evolving technologies.
In Conclusion
Software product development is a dynamic and multifaceted process that requires a blend of technical expertise, creativity, strategic planning, and effective communication. By following best practices, embracing innovation, and staying agile in response to change, organizations can create successful software products that meet the needs of users in today’s digital landscape.
7 Key Benefits of Software Product Development for Business Growth and Innovation
- Innovative solutions tailored to specific user needs.
- Enhanced efficiency and automation of business processes.
- Scalable products that can grow with the business.
- Improved customer satisfaction through user-friendly interfaces.
- Opportunities for continuous improvement and updates.
- Increased competitiveness in the market through technological advancements.
- Potential for creating new revenue streams and expanding market reach.
Top 6 Challenges in Software Product Development: Managing Complexity, Delays, Costs, Integration, Security, and Team Collaboration
- Complexity of managing project scope and requirements
- Risk of delays due to unforeseen technical challenges
- Potential for cost overruns during development and testing phases
- Difficulty in ensuring seamless integration with existing systems or third-party applications
- Challenge of maintaining software security and addressing vulnerabilities
- Strain on team collaboration and communication, especially in distributed or remote work environments
Innovative solutions tailored to specific user needs.
One of the key advantages of software product development is the ability to create innovative solutions that are customized to meet specific user needs. By understanding the unique requirements and preferences of users, developers can design and build software products that address specific challenges or provide tailored functionalities. This personalized approach not only enhances user satisfaction and engagement but also increases the overall value and effectiveness of the software solution in meeting the precise needs of its intended audience.
Enhanced efficiency and automation of business processes.
Enhanced efficiency and automation of business processes are significant benefits of software product development. By leveraging technology to streamline workflows, businesses can reduce manual tasks, minimize errors, and improve overall productivity. Automated processes not only save time but also enable employees to focus on more strategic tasks that drive innovation and growth. With custom software solutions tailored to specific business needs, organizations can optimize their operations, achieve cost savings, and gain a competitive edge in today’s fast-paced market environment.
Scalable products that can grow with the business.
Scalability in software product development offers a significant advantage by ensuring that products can expand and evolve in tandem with the growth of a business. By designing and developing scalable solutions, organizations can easily accommodate increasing user demands, new features, and higher workloads without experiencing significant disruptions or the need for a complete overhaul of the software architecture. This pro of scalability not only enhances the longevity and adaptability of software products but also enables businesses to remain agile and competitive in a rapidly changing market environment.
Improved customer satisfaction through user-friendly interfaces.
One significant benefit of software product development is the enhancement of customer satisfaction through the implementation of user-friendly interfaces. By prioritizing intuitive design and ease of use, software developers can create products that cater to the needs and preferences of users. User-friendly interfaces not only streamline the user experience but also contribute to increased engagement, efficiency, and overall satisfaction with the software. This focus on usability ultimately leads to happier customers who are more likely to continue using the product and recommend it to others, thereby fostering long-term relationships and loyalty.
Opportunities for continuous improvement and updates.
One significant advantage of software product development is the opportunities it provides for continuous improvement and updates. Through regular iterations and enhancements, developers can address user feedback, incorporate new features, fix bugs, and adapt to changing market demands. This iterative approach not only ensures that the software remains relevant and competitive but also allows for ongoing optimization of performance, functionality, and user experience. By embracing a mindset of continuous improvement, software products can evolve over time to meet the evolving needs and expectations of users, ultimately leading to greater customer satisfaction and long-term success.
Increased competitiveness in the market through technological advancements.
In the realm of software product development, one significant advantage is the ability to enhance competitiveness in the market through technological advancements. By leveraging cutting-edge technologies and innovative solutions, companies can differentiate themselves from competitors, attract a larger customer base, and stay ahead of industry trends. This proactive approach not only boosts brand visibility and credibility but also opens up new opportunities for growth and expansion in an increasingly digital-driven business landscape.
Potential for creating new revenue streams and expanding market reach.
Software product development offers a significant advantage in the potential for creating new revenue streams and expanding market reach. By introducing innovative software products tailored to meet the evolving needs of customers, businesses can tap into previously untapped markets and attract a broader audience. This expansion not only increases revenue opportunities but also enhances brand visibility and competitiveness in the industry. Through strategic product development, organizations can diversify their offerings, reach new customer segments, and ultimately drive growth and profitability.
Complexity of managing project scope and requirements
The complexity of managing project scope and requirements poses a significant challenge in software product development. As projects evolve, stakeholders may introduce new features or changes, leading to scope creep and shifting requirements. Balancing the need for innovation with the constraints of time and resources requires careful planning, communication, and prioritization. Failure to effectively manage project scope and requirements can result in delays, budget overruns, and compromised product quality. Addressing this con demands a proactive approach, clear documentation of requirements, regular stakeholder engagement, and a flexible mindset to adapt to evolving project needs while ensuring alignment with the overall project goals.
Risk of delays due to unforeseen technical challenges
One significant con of software product development is the risk of delays caused by unforeseen technical challenges. Despite meticulous planning and preparation, projects can encounter unexpected hurdles such as complex integration issues, compatibility problems, or unanticipated bugs that may disrupt the development timeline. These technical obstacles not only require additional time and resources to resolve but can also impact the overall project schedule, leading to potential delays in product delivery and increased costs. Managing and mitigating these unforeseen challenges effectively is crucial to minimizing project delays and ensuring successful software product development.
Potential for cost overruns during development and testing phases
One significant con of software product development is the potential for cost overruns during the development and testing phases. As projects progress, unforeseen challenges, changes in requirements, and technical complexities can arise, leading to delays and increased expenses. This can strain budgets and impact project timelines, making it crucial for development teams to carefully manage resources, communicate effectively with stakeholders, and implement strategies to mitigate the risk of cost overruns throughout the software development lifecycle.
Difficulty in ensuring seamless integration with existing systems or third-party applications
One significant challenge in software product development is the difficulty in ensuring seamless integration with existing systems or third-party applications. This con often arises due to differences in technology standards, data formats, and communication protocols between the new software product and the existing systems or external applications. Achieving interoperability and smooth data exchange can be a complex task that requires thorough planning, testing, and potentially custom development work to bridge the gaps between disparate systems. Failure to address integration challenges effectively can lead to compatibility issues, data inconsistencies, and overall system inefficiencies, hindering the overall performance and usability of the software product.
Challenge of maintaining software security and addressing vulnerabilities
In software product development, one significant challenge is the constant need to maintain software security and address vulnerabilities. As technology advances and cyber threats become more sophisticated, developers must stay vigilant in identifying and patching potential security loopholes in their products. Failing to address security concerns can lead to data breaches, compromised user information, financial losses, and damage to a company’s reputation. It requires ongoing efforts to implement robust security measures, conduct regular security audits, and stay informed about the latest cybersecurity trends to mitigate risks effectively.
Strain on team collaboration and communication, especially in distributed or remote work environments
One significant con of software product development is the strain it can place on team collaboration and communication, particularly in distributed or remote work environments. The physical distance between team members can hinder real-time interactions, leading to delays in decision-making, misunderstandings, and a lack of cohesive teamwork. Without face-to-face communication, the nuances of discussions and feedback may be lost, making it challenging to maintain alignment and productivity across the development process. Overcoming these obstacles requires proactive efforts to establish clear communication channels, leverage collaboration tools effectively, and foster a strong sense of team cohesion despite geographical separation.