Optimizing Business Operations with IT Infrastructure as a Service
The Power of IT Infrastructure as a Service (IaaS)
IT infrastructure is the backbone of modern businesses, enabling them to operate efficiently and effectively in today’s digital world. With the rise of cloud computing, a new model known as Infrastructure as a Service (IaaS) has revolutionized the way organizations manage their IT resources.
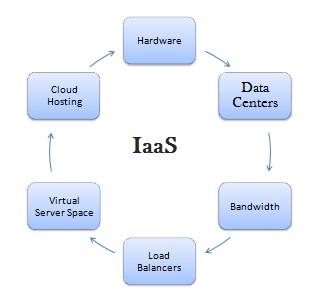
What is IaaS?
IaaS is a cloud computing service model that provides virtualized computing resources over the internet. Instead of investing in physical servers, storage, and networking equipment, businesses can leverage IaaS to access these resources on a pay-as-you-go basis.
The Benefits of IaaS
Scalability: One of the key advantages of IaaS is its scalability. Organizations can easily scale up or down their IT infrastructure based on their changing needs without the hassle of procuring and managing physical hardware.
Cost-Effectiveness: By opting for IaaS, businesses can reduce capital expenses associated with purchasing and maintaining hardware. They only pay for the resources they use, making it a cost-effective solution for both small startups and large enterprises.
Flexibility: IaaS offers flexibility in terms of resource allocation and deployment. Businesses can quickly provision virtual servers, storage, and networking components to support their applications and workloads.
Use Cases for IaaS
Development and Testing Environments: IaaS is ideal for creating development and testing environments without the need for physical infrastructure. Developers can spin up virtual servers to test applications before deploying them into production.
Disaster Recovery: Organizations can use IaaS for disaster recovery purposes by replicating their critical data and applications to cloud-based infrastructure. In case of a disaster, they can quickly restore operations from the cloud environment.
Conclusion
IaaS has transformed the way businesses approach IT infrastructure management by providing a flexible, scalable, and cost-effective solution through cloud-based services. As organizations continue to embrace digital transformation, IaaS will play a crucial role in enabling innovation and growth in the ever-evolving digital landscape.
Understanding IT Infrastructure as a Service: Key Questions Answered
- What are examples of IaaS?
- What are SaaS and examples?
- What is an eg of infrastructure as a service?
- What is IaaS and its example?
- What are the three infrastructure as a service?
- What is an IT infrastructure service?
- What is infrastructure as a service?
What are examples of IaaS?
When it comes to examples of Infrastructure as a Service (IaaS), popular cloud service providers such as Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform are often cited. These platforms offer a wide range of virtualized computing resources, including virtual servers, storage, and networking capabilities that businesses can leverage on-demand. Additionally, platforms like DigitalOcean and IBM Cloud also provide IaaS solutions tailored to meet various business needs. Overall, these examples showcase the versatility and scalability of IaaS offerings in the cloud computing landscape.
What are SaaS and examples?
Software as a Service (SaaS) is a cloud computing model that allows users to access software applications over the internet on a subscription basis. Unlike traditional software installations, SaaS eliminates the need for users to download and maintain the software on their own devices. Instead, users can simply log in to the SaaS platform through a web browser and start using the application. Examples of popular SaaS applications include Microsoft Office 365, Salesforce, Google Workspace, Dropbox, and Adobe Creative Cloud. These applications offer users flexibility, scalability, and cost-effectiveness by providing access to powerful tools and services without the burden of managing complex software installations.
What is an eg of infrastructure as a service?
Infrastructure as a Service (IaaS) offers businesses the flexibility to access virtualized computing resources over the internet, allowing them to scale their IT infrastructure based on demand. An example of IaaS is Amazon Web Services (AWS), a leading cloud service provider that offers a wide range of infrastructure services, including virtual servers, storage, and networking capabilities. With AWS, organizations can quickly provision and deploy resources without the need for upfront investment in physical hardware, making it an excellent example of how IaaS can streamline IT operations and support business growth.
What is IaaS and its example?
IaaS, short for Infrastructure as a Service, is a cloud computing service model that offers virtualized computing resources over the internet. An example of IaaS is Amazon Web Services (AWS), where businesses can access virtual servers, storage, and networking components on a pay-as-you-go basis. With IaaS, organizations can scale their IT infrastructure up or down based on their needs without the burden of managing physical hardware. This flexibility and cost-effectiveness make IaaS a popular choice for businesses looking to optimize their IT resources and focus on innovation and growth.
What are the three infrastructure as a service?
When it comes to Infrastructure as a Service (IaaS), there are three main types of services that businesses can leverage: compute, storage, and networking. Compute services provide virtualized computing resources such as virtual machines and processing power, allowing organizations to run applications and workloads in the cloud. Storage services offer scalable and secure storage solutions for data, files, and backups, eliminating the need for on-premises storage hardware. Networking services enable businesses to set up and manage virtual networks, connect resources across different locations, and ensure secure communication between cloud-based services. By utilizing these three core IaaS offerings, organizations can build flexible and efficient IT infrastructures tailored to their specific needs.
What is an IT infrastructure service?
An IT infrastructure service refers to a comprehensive set of virtualized computing resources delivered over the internet as part of the Infrastructure as a Service (IaaS) cloud computing model. It encompasses virtual servers, storage, networking components, and other IT resources that businesses can access on-demand to support their operations. By leveraging IT infrastructure services, organizations can optimize their technology environment, improve scalability and flexibility, and reduce the burden of managing physical hardware. This cloud-based approach allows businesses to focus on their core activities while relying on a reliable and cost-effective IT infrastructure solution.
What is infrastructure as a service?
Infrastructure as a Service (IaaS) is a cloud computing service model that offers virtualized computing resources over the internet. In simple terms, IaaS allows businesses to access and utilize essential IT infrastructure components such as servers, storage, and networking without the need to invest in physical hardware. By leveraging IaaS, organizations can scale their IT resources up or down based on demand, pay only for the resources they use, and enjoy the flexibility of provisioning and managing their infrastructure in a cost-effective and efficient manner.