Unlocking Success with Custom-Built Software Solutions
The Power of Custom-Built Software
In today’s fast-paced digital world, businesses are constantly seeking ways to stay ahead of the competition. One effective strategy that many successful companies are adopting is investing in custom-built software solutions tailored to their specific needs.
Custom-built software refers to applications or systems that are uniquely developed to address a company’s unique requirements and challenges. Unlike off-the-shelf software, custom solutions are designed from the ground up with the organization’s goals, processes, and workflows in mind.
Benefits of Custom-Built Software:
- Enhanced Efficiency: Custom software is built to streamline processes and automate tasks, leading to increased productivity and efficiency within the organization.
- Scalability: As businesses grow and evolve, custom software can easily be scaled to accommodate changing needs and requirements without major disruptions.
- Competitive Edge: By having software that is tailored specifically for their operations, companies can gain a competitive edge by offering unique features and capabilities that set them apart from competitors.
- Improved Security: Custom-built software can be designed with robust security measures to protect sensitive data and mitigate cybersecurity risks.
- Cost-Effectiveness: While the initial investment in custom software development may be higher than off-the-shelf solutions, in the long run, it can result in cost savings by eliminating the need for multiple third-party applications and reducing manual workarounds.
Choosing a Reliable Software Development Partner
When embarking on a custom software development project, it is crucial to partner with a reputable software development company that has a proven track record of delivering high-quality solutions. A reliable partner will work closely with your team to understand your business objectives and develop a tailored solution that meets your specific requirements.
In conclusion, custom-built software offers businesses a powerful tool for driving innovation, increasing efficiency, and gaining a competitive advantage in today’s digital landscape. By investing in bespoke solutions that align with their unique needs, organizations can position themselves for long-term success and growth.
8 Essential Tips for Successful Custom Software Development
- Clearly define your requirements before starting the development process.
- Communicate effectively with the development team to ensure alignment on project goals.
- Consider scalability and flexibility in the design to accommodate future growth.
- Regularly test the software for bugs and performance issues throughout the development cycle.
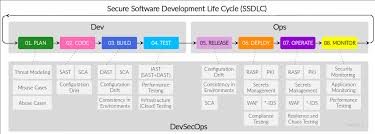
- Prioritize security measures to protect sensitive data and prevent cyber threats.
- Document all aspects of the custom software for easier maintenance and troubleshooting.
- Provide training for end-users to maximize adoption and utilization of the new software.
- Gather feedback from users to continuously improve and enhance the custom-built software.
Clearly define your requirements before starting the development process.
It is essential to clearly define your requirements before initiating the development process for custom-built software. By outlining your objectives, functionalities, and expectations upfront, you provide a roadmap for the development team to follow. This step helps ensure that the final product aligns closely with your needs and minimizes the risk of misunderstandings or costly changes later in the project. Clear requirements also facilitate effective communication between stakeholders and developers, leading to a smoother development process and a successful outcome that meets your business goals.
Communicate effectively with the development team to ensure alignment on project goals.
Effective communication with the development team is essential to ensure alignment on project goals when creating custom-built software. By maintaining clear and open lines of communication, stakeholders can convey their requirements, expectations, and feedback to the development team. This collaborative approach helps in fostering a shared understanding of the project objectives, leading to the successful delivery of a tailored software solution that meets the organization’s specific needs and vision.
Consider scalability and flexibility in the design to accommodate future growth.
When developing custom-built software, it is essential to consider scalability and flexibility in the design to accommodate future growth. By planning for scalability, organizations can ensure that the software can easily expand and adapt to meet increasing demands as the business evolves. Additionally, incorporating flexibility into the design allows for modifications and enhancements to be made efficiently, enabling the software to remain relevant and effective in the face of changing requirements. Prioritizing scalability and flexibility during the development process can help future-proof the software and support long-term success for the organization.
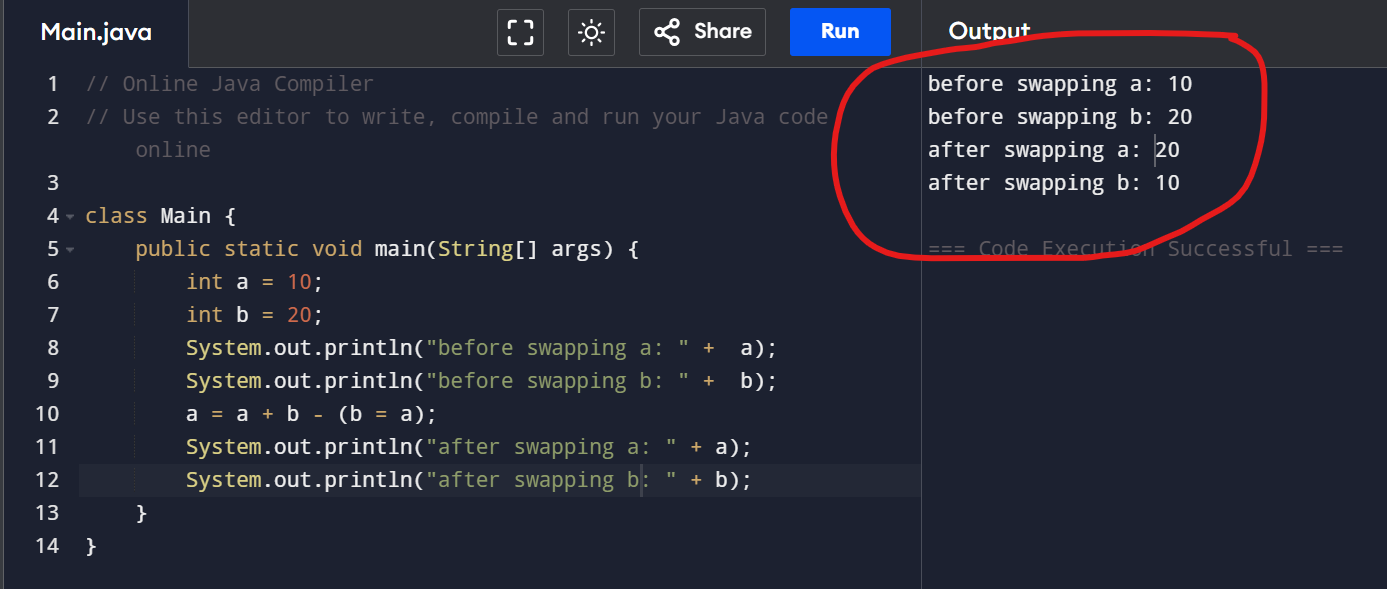
Regularly test the software for bugs and performance issues throughout the development cycle.
To ensure the success of custom-built software, it is essential to incorporate regular testing for bugs and performance issues at every stage of the development cycle. By conducting thorough testing throughout the process, developers can identify and address any issues early on, preventing potential setbacks and ensuring the final product meets quality standards. This proactive approach not only helps in delivering a reliable and high-performing software solution but also enhances user experience and overall satisfaction with the end product.
Prioritize security measures to protect sensitive data and prevent cyber threats.
It is crucial for businesses investing in custom-built software to prioritize security measures to safeguard sensitive data and prevent cyber threats. By implementing robust security protocols and encryption techniques, organizations can ensure the confidentiality and integrity of their information, mitigating the risk of data breaches and unauthorized access. Proactive measures such as regular security audits, vulnerability assessments, and employee training on cybersecurity best practices are essential components of a comprehensive security strategy that can help protect valuable data assets from potential threats.
Document all aspects of the custom software for easier maintenance and troubleshooting.
Documenting all aspects of custom-built software is crucial for ensuring easier maintenance and troubleshooting in the long run. Comprehensive documentation that outlines the software’s architecture, functionalities, dependencies, and any customizations made during development provides valuable insights for developers and IT teams. By maintaining detailed documentation, organizations can streamline future updates, identify issues more efficiently, and facilitate knowledge transfer among team members. This proactive approach to documentation not only enhances the software’s maintainability but also contributes to overall system reliability and performance.
Provide training for end-users to maximize adoption and utilization of the new software.
Providing training for end-users is a crucial step in maximizing the adoption and utilization of custom-built software within an organization. By offering comprehensive training sessions, employees can gain the necessary skills and knowledge to effectively use the new software, leading to increased efficiency and productivity. Training also helps to minimize resistance to change and ensures that users feel confident and empowered when working with the customized solution. Ultimately, investing in training for end-users not only enhances the overall success of the software implementation but also fosters a culture of continuous learning and improvement within the organization.
Gather feedback from users to continuously improve and enhance the custom-built software.
To ensure the success and effectiveness of custom-built software, it is essential to gather feedback from users on a regular basis. By soliciting input from those who interact with the software daily, developers can gain valuable insights into how the system is being used, what features are most beneficial, and where improvements can be made. This feedback loop allows for continuous enhancement and refinement of the custom software, ensuring that it remains aligned with user needs and evolves to meet changing requirements over time.