Enhancing Cyber Defense: Network Security Consulting Services for Your Business
The Importance of Network Security Consulting Services
In today’s digital age, network security is crucial for businesses of all sizes. With the increasing number of cyber threats and attacks, companies need to prioritize protecting their sensitive data and ensuring the integrity of their networks. This is where network security consulting services play a vital role.
What Are Network Security Consulting Services?
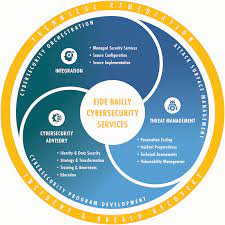
Network security consulting services involve assessing, designing, implementing, and managing security measures to protect a company’s network infrastructure. These services are provided by experts in the field who have the knowledge and experience to identify vulnerabilities and recommend solutions to mitigate risks.
The Benefits of Network Security Consulting Services
By partnering with a network security consulting firm, businesses can:
- Identify Vulnerabilities: Consultants conduct thorough assessments to identify weaknesses in the network that could be exploited by hackers.
- Implement Protective Measures: They recommend and implement security measures such as firewalls, encryption, intrusion detection systems, and access controls to safeguard the network.
- Stay Ahead of Threats: Consultants stay updated on the latest cyber threats and trends, enabling them to proactively protect the network from emerging risks.
- Comply with Regulations: They help businesses comply with industry regulations and data protection laws by ensuring that their network security measures meet required standards.
- Provide Expert Guidance: Consultants offer expert advice on best practices for network security and assist in developing customized security strategies tailored to the specific needs of the business.
Choosing the Right Network Security Consulting Firm
When selecting a network security consulting firm, businesses should consider factors such as:
- Experience: Look for a firm with a proven track record in providing effective network security solutions.
- Certifications: Check if consultants hold relevant certifications in cybersecurity and information technology.
- Client Reviews: Read reviews and testimonials from previous clients to gauge satisfaction levels.
- Customized Solutions: Ensure that the firm offers tailored solutions that address your specific security needs.
In Conclusion
In conclusion, investing in network security consulting services is essential for safeguarding your business against cyber threats. By partnering with experienced consultants, you can strengthen your network defenses, protect your valuable data, and ensure continuity of operations in an increasingly interconnected world.
Top 5 Essential Tips for Enhancing Network Security Consulting Services
- Perform regular security assessments to identify vulnerabilities
- Implement strong authentication methods for access control
- Encrypt sensitive data both in transit and at rest
- Establish a robust incident response plan for quick mitigation of security breaches
- Stay updated on the latest security threats and best practices
Perform regular security assessments to identify vulnerabilities
Performing regular security assessments is a crucial aspect of network security consulting services. By conducting thorough assessments, businesses can proactively identify vulnerabilities in their network infrastructure before they are exploited by cyber threats. This proactive approach allows companies to implement necessary security measures to strengthen their defenses and mitigate potential risks effectively. Regular security assessments not only help in maintaining a secure network environment but also ensure compliance with industry regulations and data protection standards.
Implement strong authentication methods for access control
Implementing strong authentication methods for access control is a crucial step in enhancing network security. By requiring multiple factors for user authentication, such as passwords, biometrics, or security tokens, organizations can significantly reduce the risk of unauthorized access to sensitive data and systems. Strong authentication adds an extra layer of protection against cyber threats and helps ensure that only authorized individuals can access critical resources within the network. This proactive approach to access control is essential in today’s threat landscape to prevent potential security breaches and safeguard valuable information from malicious actors.
Encrypt sensitive data both in transit and at rest
Encrypting sensitive data both in transit and at rest is a critical practice recommended by network security consulting services. By implementing encryption protocols, businesses can ensure that data remains secure and protected from unauthorized access whether it is being transmitted between devices or stored on servers or databases. This added layer of security helps mitigate the risk of data breaches and safeguards confidential information, enhancing overall network security posture.
Establish a robust incident response plan for quick mitigation of security breaches
Establishing a robust incident response plan is a critical aspect of network security consulting services. By having a well-defined plan in place, businesses can effectively and efficiently respond to security breaches, minimizing the impact of potential threats. A proactive incident response strategy not only helps in containing the breach but also aids in identifying the root cause and implementing necessary measures to prevent future incidents. Quick mitigation of security breaches is essential to maintaining the integrity and security of a company’s network infrastructure.
Stay updated on the latest security threats and best practices
It is crucial for businesses utilizing network security consulting services to stay informed about the latest security threats and best practices. By remaining updated on emerging cyber threats and industry best practices, companies can proactively enhance their network defenses and mitigate potential risks. This proactive approach not only helps in preventing security breaches but also ensures that the implemented security measures are aligned with current cybersecurity standards, ultimately strengthening the overall security posture of the organization.