Enhancing SaaS Cyber Security: Best Practices for Data Protection
The Importance of SaaS Cyber Security
Software as a Service (SaaS) has become increasingly popular among businesses for its convenience and scalability. However, with the rise of SaaS applications comes the need for robust cyber security measures to protect sensitive data and ensure business continuity.
Why SaaS Cyber Security Matters
Securing SaaS applications is crucial to safeguarding valuable information stored in the cloud. Cyber threats such as data breaches, ransomware attacks, and phishing scams pose significant risks to organizations that rely on SaaS solutions.
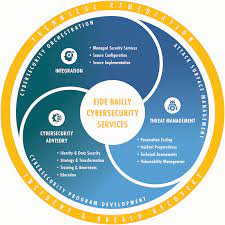
Key Aspects of SaaS Cyber Security
Effective SaaS cyber security involves implementing various measures to mitigate risks and prevent unauthorized access to data. Some key aspects include:
- Data Encryption: Encrypting data both in transit and at rest helps protect information from being intercepted or compromised.
- Multi-Factor Authentication: Implementing multi-factor authentication adds an extra layer of security by requiring users to provide multiple forms of verification.
- Regular Security Audits: Conducting regular security audits helps identify vulnerabilities and ensure compliance with industry standards.
- Employee Training: Educating employees about best practices for data security and how to recognize potential threats can help prevent cyber attacks.
- Incident Response Plan: Having a well-defined incident response plan in place enables organizations to respond quickly and effectively in the event of a security breach.
The Future of SaaS Cyber Security
As technology continues to evolve, so do cyber threats. It is essential for organizations to stay vigilant and proactive in enhancing their SaaS cyber security posture. By investing in robust security measures and staying informed about emerging threats, businesses can better protect their data and maintain the trust of their customers.
7 Key Advantages of SaaS Cybersecurity: Boosting Protection and Efficiency
- Enhanced Data Security
- Scalability
- Cost-Effective
- Automatic Updates
- Accessibility
- Compliance Assurance
- Disaster Recovery
Top 7 Concerns About SaaS Cybersecurity: What You Need to Know
- Dependency on Service Provider
- Data Privacy Concerns
- Limited Control
- Internet Connectivity Dependency
- Shared Resources
- Vendor Lock-in
- Security Incidents Impact Multiple Users
Enhanced Data Security
Enhanced data security is a significant advantage of SaaS cyber security measures. By implementing robust security protocols, SaaS applications ensure that sensitive data is safeguarded against unauthorized access. This protection is crucial in today’s digital landscape, where data breaches and cyber attacks are prevalent threats. With SaaS cyber security in place, organizations can have peace of mind knowing that their valuable information is well-protected, maintaining the trust of their customers and stakeholders.
Scalability
Scalability is a significant advantage of SaaS cyber security, allowing businesses to adapt and expand their security measures seamlessly as they grow and evolve. With SaaS solutions, organizations can easily adjust their security protocols to accommodate increased data volumes, user access levels, and changing business needs. This flexibility ensures that businesses can maintain a strong and effective security posture throughout their growth journey without significant disruptions or delays.
Cost-Effective
Implementing SaaS cyber security is a cost-effective solution that offers significant savings compared to establishing and managing in-house security infrastructure. By leveraging SaaS services, businesses can benefit from advanced security measures without the hefty upfront costs associated with building and maintaining their own security systems. This cost-efficient approach allows organizations to allocate resources more efficiently, focusing on core business activities while ensuring robust protection against cyber threats.
Automatic Updates
SaaS providers offer a significant advantage in terms of cyber security through automatic updates. By consistently updating their security features to address new threats and vulnerabilities, SaaS providers ensure that their clients’ data remains protected against evolving cyber risks. This proactive approach to security maintenance not only saves businesses time and resources but also enhances their overall resilience to potential cyber attacks. Automatic updates play a crucial role in keeping SaaS applications secure and up-to-date, providing peace of mind to users knowing that they are always equipped with the latest defense mechanisms against emerging threats.
Accessibility
The accessibility aspect of SaaS cyber security offers users the convenience of accessing secure applications from any location with an internet connection. This flexibility allows users to work remotely, collaborate seamlessly, and stay productive without being tied to a specific physical location. By enabling users to access software and data securely from anywhere, SaaS enhances efficiency and agility within organizations while maintaining robust security measures to protect sensitive information.
Compliance Assurance
Compliance assurance is a significant advantage of SaaS cyber security as many SaaS providers diligently adhere to industry regulations and standards. By following established guidelines, SaaS providers help businesses ensure compliance with data protection laws and other regulatory requirements. This proactive approach not only helps organizations avoid costly penalties but also instills trust among customers and stakeholders, demonstrating a commitment to safeguarding sensitive information and maintaining high standards of security.
Disaster Recovery
SaaS solutions offer a valuable pro in the form of disaster recovery capabilities. These platforms typically come equipped with robust backup and recovery features that play a critical role in safeguarding data during emergencies or unforeseen events. By leveraging these built-in tools, businesses can ensure that their information remains secure and accessible even in the face of disasters, helping them maintain continuity and minimize potential disruptions to their operations.
Dependency on Service Provider
Organizations face a significant con of SaaS cyber security in the form of dependency on the service provider for security measures. This reliance introduces a potential risk, especially when the provider’s security practices are insufficient or inadequate. In such cases, organizations may find themselves vulnerable to cyber threats and data breaches that could have been prevented with more robust security protocols in place. The lack of control over the security practices of the SaaS provider underscores the importance for organizations to thoroughly vet and assess the security capabilities of their service providers to mitigate this inherent risk.
Data Privacy Concerns
Storing sensitive data in the cloud raises significant data privacy concerns for organizations utilizing SaaS solutions. The potential risk of unauthorized access to confidential information stored in the cloud poses a threat to data privacy and can lead to compliance issues with regulations such as GDPR and HIPAA. Ensuring that data is securely handled and protected from cyber threats is crucial to maintaining trust with customers and meeting regulatory requirements in an increasingly data-sensitive environment. Organizations must address these data privacy concerns proactively by implementing robust security measures and encryption protocols to safeguard sensitive information stored in the cloud.
Limited Control
Organizations utilizing Software as a Service (SaaS) solutions may encounter the con of limited control over the security protocols and infrastructure provided by the SaaS provider. This lack of control can pose challenges for organizations that have specific security requirements or compliance standards to meet. Without the ability to directly manage or customize security measures, businesses may feel vulnerable to potential risks and find it difficult to address security concerns that are not within their control. It is crucial for organizations to carefully assess and negotiate security agreements with SaaS providers to ensure that their data remains protected and compliant with industry regulations.
Internet Connectivity Dependency
Access to SaaS applications is crucial for modern businesses, but one significant con of SaaS cyber security is the dependency on internet connectivity. Organizations relying on SaaS solutions are vulnerable to disruptions caused by internet outages or connectivity issues. Any interruption in internet access can hinder productivity and impact business operations, highlighting the importance of having contingency plans in place to mitigate the risks associated with this dependency.
Shared Resources
In SaaS environments, one significant con of cyber security is the concept of shared resources due to multi-tenancy. When resources are shared among multiple users, there is a higher risk of data exposure. This shared infrastructure can create vulnerabilities that may be exploited by malicious actors, leading to potential breaches and unauthorized access to sensitive information. Organizations must carefully assess and manage the risks associated with shared resources in SaaS environments to ensure the protection of their data and maintain a secure operating environment.
Vendor Lock-in
Vendor lock-in is a significant con of SaaS cyber security, as it can restrict businesses from easily switching between providers. This limitation not only hinders flexibility but also poses potential security risks when considering a change in SaaS vendors. Organizations may find themselves locked into a specific provider’s ecosystem, making it challenging to migrate data and applications to a different platform without encountering compatibility issues or data security vulnerabilities. The lack of portability and interoperability in SaaS solutions due to vendor lock-in can impede businesses from adapting to evolving security needs and exploring alternative options for better cyber security measures.
Security Incidents Impact Multiple Users
A significant drawback of SaaS cyber security is that security incidents have the potential to impact multiple users at once. When a security breach occurs in a SaaS application, the repercussions can be widespread, affecting numerous users simultaneously. This amplifies the consequences for organizations, as the compromised data or system vulnerability may have far-reaching effects on business operations and data integrity. The interconnected nature of SaaS platforms means that a single breach can have a cascading impact, underscoring the importance of robust security measures to protect both individual users and the organization as a whole.